Digital Identity Verification Software for Enterprise Security
Verify identities, eliminate impersonation risk, and secure access across every digital touchpoint.
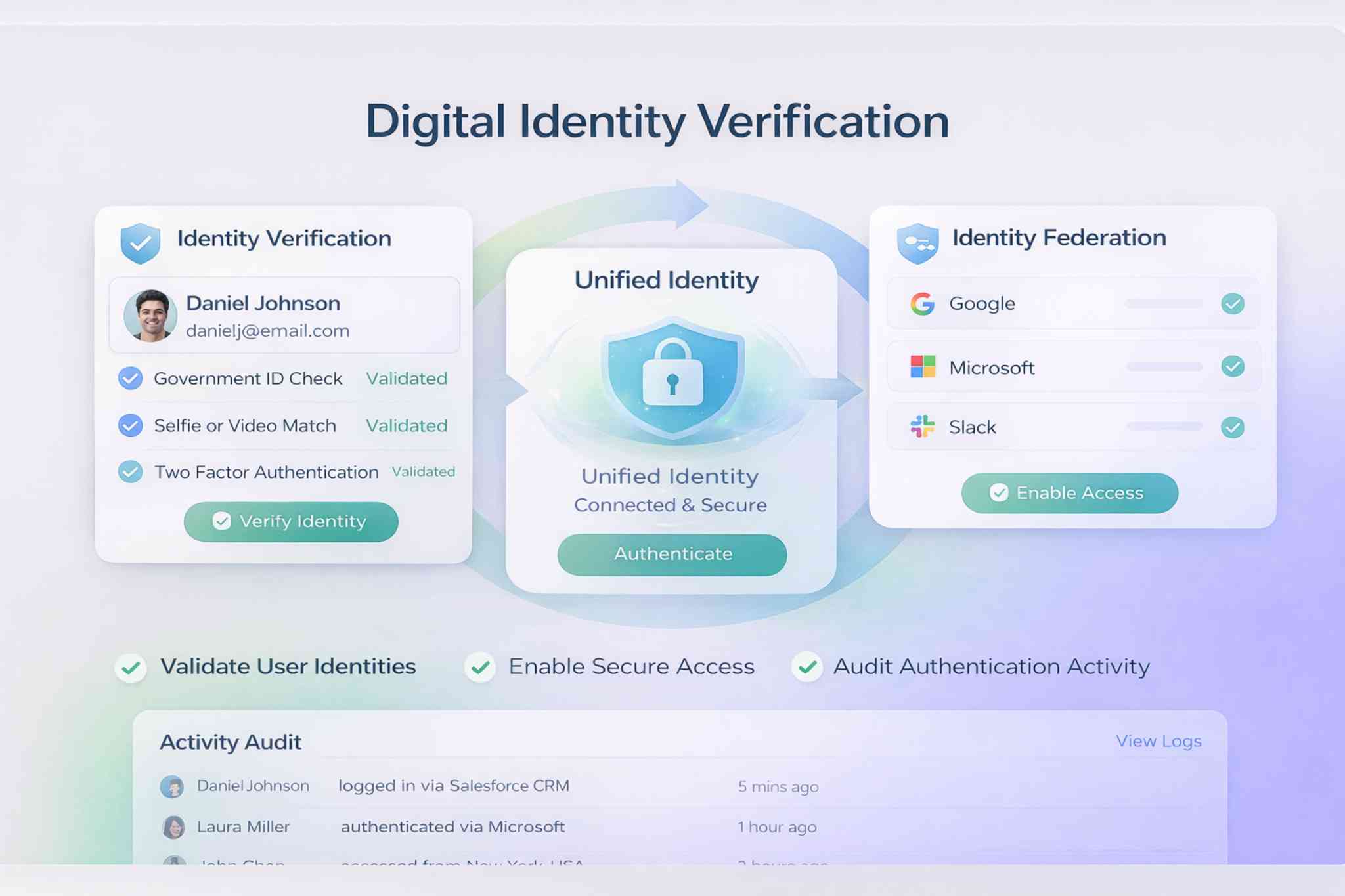
Verify Digital Identities With Confidence
Digital identity verification software ensures users are who they claim to be.
Validate user identity during account creation
The platform enables you to validate user identity during account creation so identity assurance becomes consistent and enforceable.
Enforce multi-step identity verification processes
Apply multi-step identity verification processes that strengthen digital identity validation across user accounts.
Monitor identity verification outcomes in real time
Monitor identity verification outcomes in real time while maintaining structured verification audit trails.
Apply risk-based verification rules
Apply risk-based verification rules so identity assurance becomes consistent and enforceable.
Enable Secure Identity Federation Across Systems
Identity federation software allows trusted authentication across multiple platforms.
Authenticate users once across federated systems
The system allows you to authenticate users once across federated systems.
Establish trust relationships between applications
Establish trust relationships between applications and centralize identity records across environments.
Enforce unified access policies
Enforce unified access policies that govern authentication across federated systems.
Track federated authentication activity
Track federated authentication activity so cross-system access becomes seamless and secure.
Strengthen Authentication and Authorization Controls
Digital identity verification must integrate with broader security frameworks.
Role-based authorization controls
The platform supports role-based authorization controls.
Context-aware access enforcement
The platform supports context-aware access enforcement.
Centralized permission management
The platform supports centralized permission management.
Monitoring of identity-related risk signals
Monitoring of identity-related risk signals and executive-level identity governance dashboards makes identity protection proactive rather than reactive.
Improve Compliance and Regulatory Alignment
Identity governance must support audit and compliance frameworks.
- Maintain structured identity documentation
- Log authentication and verification events
- Track identity lifecycle changes
- Consolidate multi-entity identity oversight
- Deliver compliance-ready reporting summaries
Built Directly Into Salesforce
Because the platform operates natively on Salesforce:
- Identity verification connects directly to user profiles
- Federated authentication integrates with CRM workflows
- Access updates reflect instantly
- Role-based permissions enforce governance
- No external identity verification systems are required
- Identity management becomes embedded within operational infrastructure.
AI-Powered Identity Intelligence
As authentication data expands, predictive insights strengthen security.
AI-Powered Identity Intelligence
Identity protection evolves continuously with data.
Detect suspicious identity patterns
Detect suspicious identity patterns.
Identify potential impersonation risks
Identify potential impersonation risks.
Forecast high-risk authentication attempts
Forecast high-risk authentication attempts.
Recommend identity policy adjustments
Recommend identity policy adjustments and improve long-term trust validation accuracy.
