User Access Review With Executive Accountability
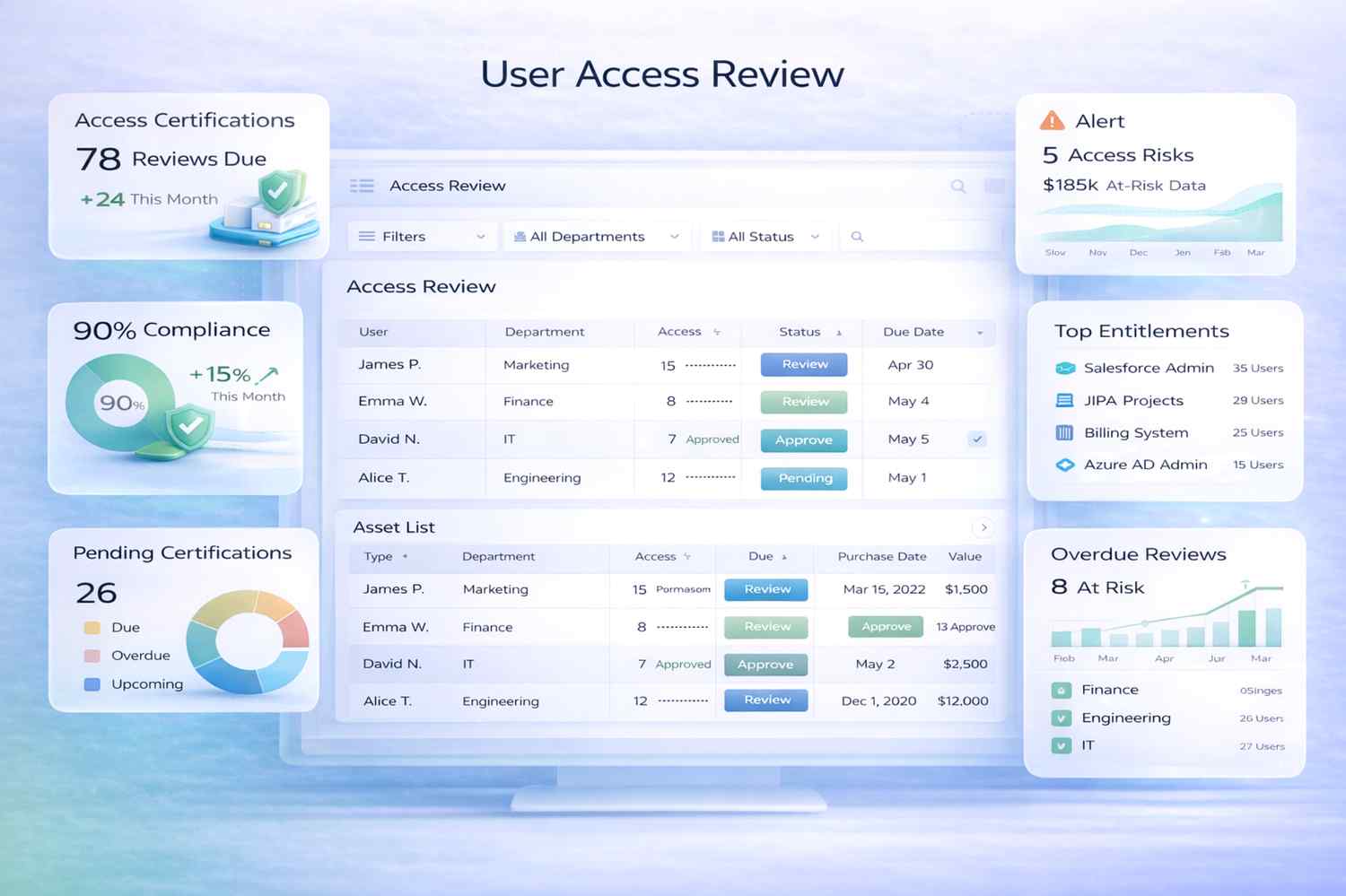
Live dashboards, risk scoring, and measurable compliance posture. Centralize access certifications, monitor permission changes, and enforce least-privilege controls directly inside Salesforce.
Centralize User Access Management
User access management software ensures permissions are centrally governed and consistently enforced across departments and systems.
Consolidated Access Visibility
View access rights across departments and systems from a single centralized dashboard.
Role-Based Permission Control
Assign role-based permissions to ensure consistent access policies across teams.
Real-Time Permission Tracking
Track permission changes and adjustments instantly as access roles evolve.
Least-Privilege Enforcement
Apply least-privilege access policies to reduce operational and security risks.
Automate Access Certification Cycles
Access certification software formalizes review cycles to ensure permissions remain compliant and appropriate.
Scheduled Access Reviews
Schedule recurring access certification cycles to maintain compliance oversight.
Manager Review Workflows
Route certification tasks to managers and system owners automatically.
Approval and Revocation Tracking
Track access approvals and revocations across certification processes.
Audit-Ready Documentation
Maintain structured documentation of certification results for compliance audits.
Manage Permission Assignments and Adjustments
Permission management software centralizes the control of sensitive privileges and operational roles.
Permission Templates
Create standardized permission templates for consistent role assignments.
High-Risk Role Monitoring
Monitor sensitive roles and privileged accounts to prevent unauthorized access.
Conditional Access Policies
Apply dynamic policies based on risk levels or organizational requirements.
Segregation of Duties
Track role conflicts and enforce separation of duties across departments.
Streamline Access Requests With Governance Controls
Access request management ensures new permissions follow structured governance and approval workflows.
Digital Access Requests
Submit and track access requests through centralized digital workflows.
Risk-Based Approvals
Route approval workflows based on role sensitivity or risk levels.
Automated Access Logging
Log all permission changes automatically for compliance traceability.
Approval SLA Monitoring
Monitor approval timelines to ensure timely access provisioning.
Align Access Reviews With Compliance and Risk Frameworks
Access review software integrates identity governance directly into enterprise compliance programs with centralized audit trails and reporting.
Built Directly Into Salesforce
Because the platform operates natively on Salesforce, access governance integrates directly with operational infrastructure and identity management systems.
AI-Powered Access Risk Intelligence
AI-driven insights continuously monitor access patterns, detect governance risks, and recommend permission optimizations as identity data grows.
